Last Updated on September 30, 2022
If you are using AWS Single Sign-On (SSO) and you plan to use a Permission Set in multiple AWS accounts and will be using Customer Managed Policies, it’s annoying that you actually have to create a Customer Manage IAM Policy in each of your target AWS Account, before you could use it.
Weirdly, this is not aligned with the AWS SSO’s goal, which is to centrally manage access across multiple accounts.
By the way, AWS SSO was recently renamed AWS IAM Identity Center. But I’m still going to refer to it here as AWS SSO because that’s what I am used to.
For the fun of it, I actually tried creating IAM policies with the same name in multiple AWS accounts but with different permissions and AWS SSO accepted my permission set with customer managed policies.
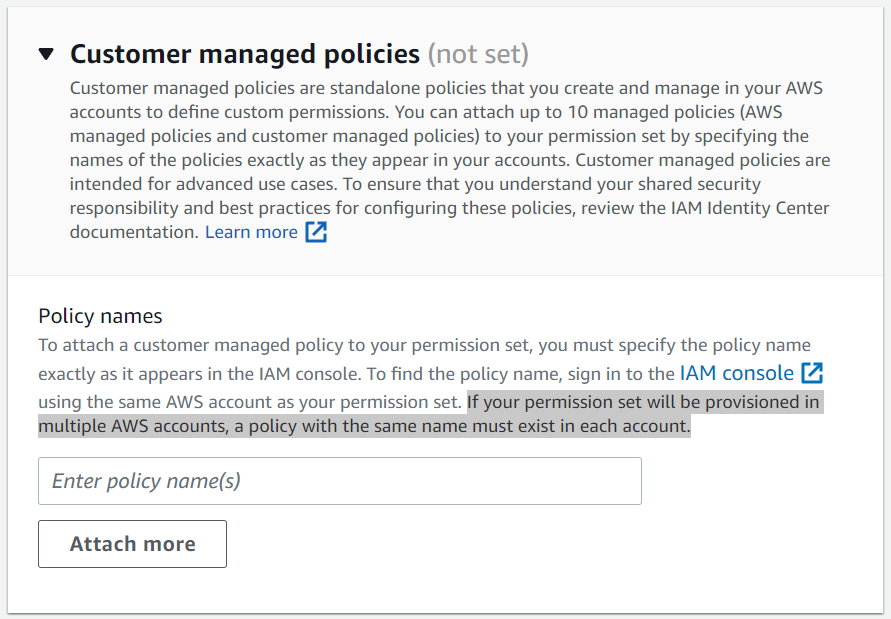
You do not have to create the IAM custom policy in the Management Account nor in the SSO Delegated Administrator account for Customer Managed Policies to work. You only have to create the IAM custom policy with the same name in the target AWS accounts.
How can we centrally configure user access without the additional overhead of maintaining IAM policies across multiple accounts?
The solution to this problem is to use Inline Policies in the Permission Set.
AWS actually encouraged using Inline Policies when you create Custom Permission Sets.
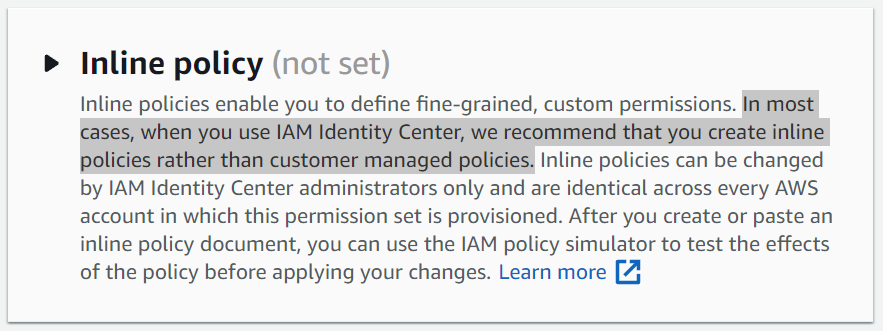
With Inline Policies on the Permission Set, whenever you modify the Inline Policy, AWS SSO will automatically update the corresponding IAM Role Inline Policy in the target AWS accounts.
Character Limits
If you want to use Inline Policies, you are bound by the IAM and STS character limits for IAM Roles, which are 10,240 characters.
You can only have one Inline Policy per Permission Set, so that is all the characters you have to work with, which is actually pretty plenty already.
For Customer Managed Policy, you are limited to 6,144 characters per policy. But you can attach up to 10 managed policies per permission set. That’s 10 combinations of AWS Managed Policies and Customer Managed Policies. Which gives you 61,440 characters to work with.
But you can actually use Inline Policy, AWS Managed Policies and Customer Managed Policies at the same time in your Permission Set so it’s up to you how to combine this and maximize the permissions.
TIP: Try to use AWS Managed Policies first, if that doesn’t work then use Inline Policies. If that still doesn’t work, good luck with using Customer Managed Policies.
So always use Inline Policies for IAM Identity Center instead of Customer Managed Policies unless you have a really good reason to use a Customer Managed Policy.
Let me know your experience with AWS SSO Permission Sets below.